Attribute-Based Access Control (ABAC)
What is ABAC?
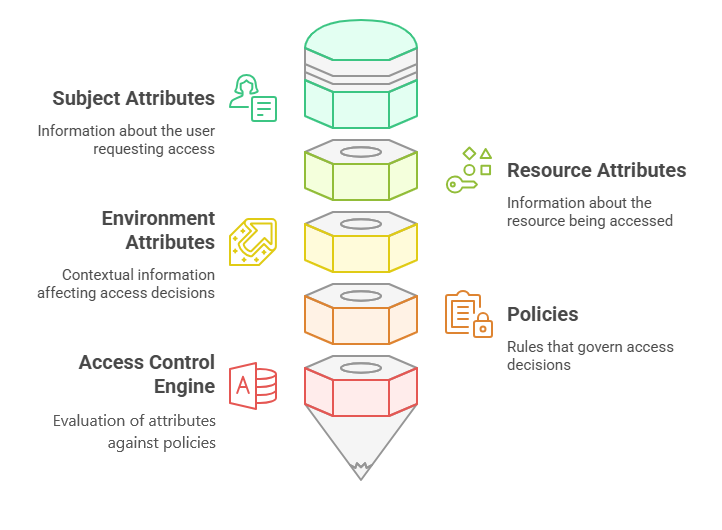
Attribute-Based Access Control (ABAC) is an access control model that grants or denies access to resources based on a set of attributes associated with the user, the resource, and the environment. These attributes can be the user identity, role, department, job function, location, time of day, and more.
How ABAC works?
Here's a high-level overview of the ABAC process:
- Attribute collection: The system collects attributes from various sources, such as user directories, databases, and environmental sensors.
- Policy evaluation: The system evaluates the collected attributes against a set of policies defined by the organization.
- Access decision: Based on the policy evaluation, the system grants or denies access to the requested resource.
How does ABAC work in Stormshield Encryption Platform?
When encrypting data with Stormshield SDK, you can attach attributes to the data. These attributes may describe the data itself or provide contextual information about the data’s environment.
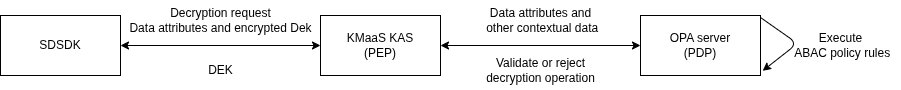
To decrypt data in ZTDF format, the encrypted Data Encryption Key (DEK) is sent to the Key Acess Server (KAS), together with the data attributes.
The KAS functions as the Policy Enforcement Point (PEP), while the attributes (and additional information such as the JWT token payload) are forwarded to the Policy Decision Point (PDP), which validates or rejects the DEK decryption request.
The PDP applies the ABAC policy rules, examining the supplied attributes to either validate or reject the DEK decryption request.
For more details on how ABAC works in KAS, please refer to the KMaaS service documentation: